HPE Juniper Networking Advanced Threat Prevention
A cloudbased service or on-premises appliance that provides complete advanced malware detection and prevention.
Overview:
Customers looking to identify and block known and unknown threats can add HPE Juniper Networking® Advanced Threat Prevention (ATP) to their HPE Juniper Networking SRX Series Services Gateways. HPE Juniper Networking ATP uses machine learning to find and block both known and unknown cyberthreats, analyzing files and network traffic looking for signs of malicious behavior. ATP can uncover zero-day malware threats and malicious connections, including botnets and C&C servers hiding in encrypted traffic. Using SecIntel, HPE Juniper Networking’s curated security intelligence feeds, ATP stops these threats in their tracks by enforcing protection mechanisms at all network connection points.
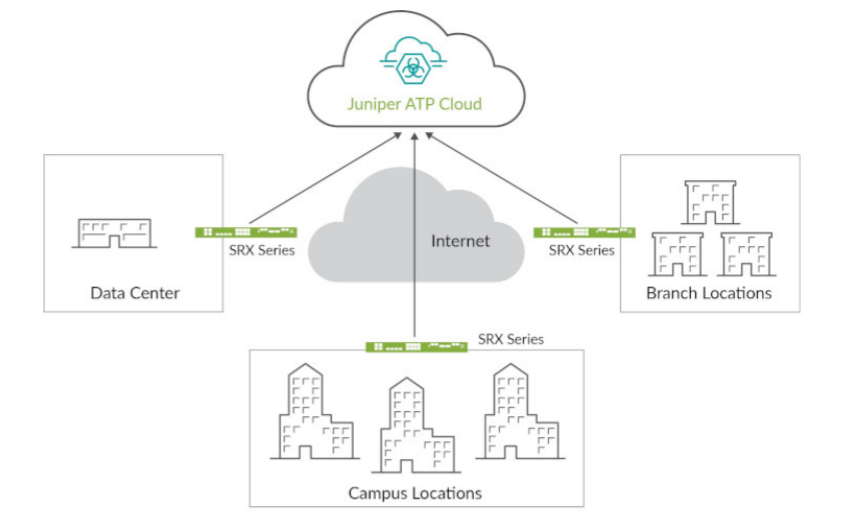
Advanced Threat Prevention Cloud
Deployed as an add-on license to an SRX Series Services Gateway, ATP Cloud uses a combination of static and dynamic analysis and machine learning to quickly identify unknown threats, either downloaded from the web or sent via e-mail, and delivers a file verdict and risk score back to the SRX Series firewall to enable blocking at the network level. In addition, ATP Cloud delivers SecIntel security intelligence consisting of malicious domains, URLs, and IP addresses gathered from file analysis, HPE Juniper Networking Threat Labs research, and highly reputable third-party threat feeds. These feeds are collected and distributed to SRX Series firewalls and HPE Juniper Networking MX Series Universal Routing Platforms to automatically block command-and-control communications, making it more difficult to wage a successful attack on the organization. ATP Cloud includes its own management portal configuration management, licensing, and reporting.
Advanced Threat Prevention Appliance
To address the needs for on-premises and virtual deployments, the ATP offering is also available on two hardware-based platforms: the HPE Juniper Networking JATP400 and JATP700 Advanced Threat Prevention Appliances.
- JATP400: The JATP400 is a 1 U appliance that delivers up to 50,000 object detonations per day. It’s purpose-built for organizations that need distributed detection of Web, e-mail, and lateral threats across the enterprise.
- JATP700: The JATP700 is a 2 U appliance for larger, centralized environments with high-performance security demands requiring up to 130,000 object detonations per day.